index_80
Router Security Configuration Guide
UNCLASSIFIED
80
UNCLASSIFIED
Version 1.0g
! the Stacheldraht DDoS system
access-list 170 deny tcp any any eq 16660 log
access-list 170 deny tcp any any eq 65000 log
! the TrinityV3 system
access-list 170 deny tcp any any eq 33270 log
access-list 170 deny tcp any any eq 39168 log
! the Subseven DDoS system and some variants
access-list 170 deny tcp any any range 6711 6712 log
access-list 170 deny tcp any any eq 6776 log
access-list 170 deny tcp any any eq 6669 log
access-list 170 deny tcp any any eq 2222 log
access-list 170 deny tcp any any eq 7000 log
The Tribe Flood Network (TFN) DDoS system uses ICMP Echo Reply messages,
which are problematic to block because they are the heart of the ping program.
Follow the directions in the ICMP sub-section, above, to prevent at least one
direction of TFN communication.
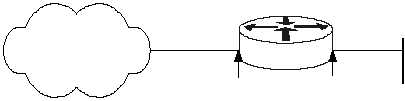
4.3.4. Example Configuration File
The configuration file shown below is not a complete configuration file. Rather, it
provides an example for using access lists on a Cisco router. The diagram below
shows the topology that this file is based on. The security policy implemented with
the access lists allows most traffic from the internal network to the external network.
The policy restricts most traffic from the external network to the internal network.
Other
Networks
East
14.1.1.20/16
14.2.6.250/24
Protected
Network
14.2.6.0/24
Interface Eth 1
Interface Eth 0
hostname East
!
interface Ethernet0
description Outside interface to the 14.1.0.0/16 network
ip address 14.1.1.20 255.255.0.0
ip access-group 100 in
!
interface Ethernet1
description Inside interface to the 14.2.6.0/24 network
ip address 14.2.6.250 255.255.255.0
ip access-group 102 in
!
router ospf 44