ICMP_Scanning_11
ICMP Usage in Scanning
11
Copyright � Ofir Arkin, 2000
http://www.sys-security.com
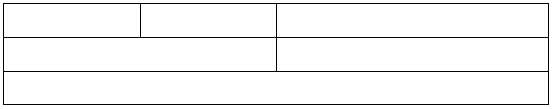
Checksum
Sequence Number
Identifier
Code
Type
0
4
8
16
31
Subnet address mask
Figure 4: ICMP Address Mask Request & Reply message format
RFC 1122 states that a system that has implemented ICMP Address Mask messages must not
send an Address Mask Reply unless it is an authoritative agent for address masks.
Usually an Address Mask request would be answered by a gateway.
Receiving an Address Mask Reply from a host would reveal an alive host that is an authoritative
agent for address masks. It will also allow a malicious computer attacker to gain knowledge about
your network’s configuration. This information can assist the malicious computer attacker in
determining your internal network structure, as well as the routing scheme.
Please note that a Router must implement ICMP Address Mask messages. This will help identify
routers along the path to the targeted network (it can also reveal internal routers if this kind of
traffic is allowed to reach them).
If the Router is following RFC 1812 closely, it should not forward on an Address Mask Request to
another network.
ICMP Address Mask Request aimed at a LINUX machine would not trigger an ICMP Address
Mask Reply, nor a request aimed at a Microsoft Windows box.
In the next example I have sent an ICMP Address Mask Request to the broadcast address
(192.168.5.255) of a class C network 192.168.5.0, spoofing the source IP to be 192.168.5.3:
[root@stan /root]# icmpush -vv -mask -sp 192.168.5.3 192.168.5.255
-> ICMP total size = 12 bytes
-> Outgoing interface = 192.168.5.1
-> MTU = 1500 bytes
-> Total packet size (ICMP + IP) = 32 bytes
ICMP Address Mask Request packet sent to 192.168.5.255 (192.168.5.255)
Receiving ICMP replies ...
-----------------------------------------------------
192.168.5.3 ...
Type = Address Mask Request (0x11)
Code = 0x0
Checksum = 0xBF87
Id = 0x3B7
Seq# = 0x3CB0
-----------------------------------------------------
icmpush: Program finished OK